Here is a little community gift for the new year (2017). Azure Stack expert Ruud Borst (@Ruud_Borst) recently published a blog post titled “Expose the Azure Stack Portal through NAT”. Ruud included a PowerShell script in this blog post that simplifies extending external access to Azure Stack.
The PowerShell script runs on your Azure Stack host and will make the IP mappings in NAT on MAS-BGPNAT01 to expose your Azure Stack instance externally to your network.
We no longer have to work through a bunch of tedious steps to give external access to Azure Stack. Thanks Ruud! Great example of community power. With Ruud’s script it can be done even if you already have Azure Stack deployed. The link to his blog post and script is here:
https://azurestack.eu/2016/12/expose-portal-azurestack-through-nat
Running the script is as easy as running something like this:
.\Expose-AzureStackPortal.ps1 -PortalExternalIP YOURFIRSTIPHERE -ACSExternalIP YOURSECONDIPHERE
Add -AppServiceAPIExternalIP if you are using the App Service RP you will need to specify a 3rd IP. SQL and MySQL both use the -PortalExternalIP so no need for an extra IP for these.
A successful run of the script should look like this:
VERBOSE: Created NAT external addresses 192.168.1.40 and 192.168.1.45 for Portal and ACS.
VERBOSE: Created Static NAT port mappings on 192.168.1.40 to 192.168.102.7 for Portal
VERBOSE: Created Static NAT port mappings on 192.168.1.40 to 192.168.102.12 for XRP
VERBOSE: Created Static NAT port mappings on 192.168.1.45 to 192.168.102.3 for ACS
VERBOSE: Created Static NAT port mappings on 192.168.1.40 to 192.168.102.14 for SQLrp
VERBOSE: Created Static NAT port mappings on 192.168.1.40 to 192.168.102.1 for MySQLrp
The last step in this process is to make sure you add the DNS records on your external network or to the host file on external servers or clients. Ruud explains this in his blog. I extended Azure Stack to my Buchatech lab environment so I went the DNS route.
For DNS entries I used a CSV file and PowerShell to import all of the DNS records I needed for Azure Stack. I used a PowerShell script from a fellow MVP. The blog post with that script can be found here:
http://www.lazywinadmin.com/2012/10/create-dns-entries-using-powershell-and.html
Here is what the CSV file should look like:
| name | ip | type | zone | dnsserver |
| portal | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| api | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| xrp.tenantextensions | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| keyvault.tenantextensions | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| health.adminextensions | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| compute.adminextensions | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| network.adminextensions | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| storage.adminextensions | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| *.blob | 192.168.1.45 | A | azurestack.local | dc.buchatech.com |
| *.queue | 192.168.1.45 | A | azurestack.local | dc.buchatech.com |
| *.table | 192.168.1.45 | A | azurestack.local | dc.buchatech.com |
| sqlrp | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| mysqlrp | 192.168.1.40 | A | azurestack.local | dc.buchatech.com |
| A | azurestack.local | dc.buchatech.com | ||
| A | azurestack.local | dc.buchatech.com | ||
| A | azurestack.local | dc.buchatech.com | ||
| A | azurestack.local | dc.buchatech.com |
Here is the CSV file I used so you don’t have to create it.
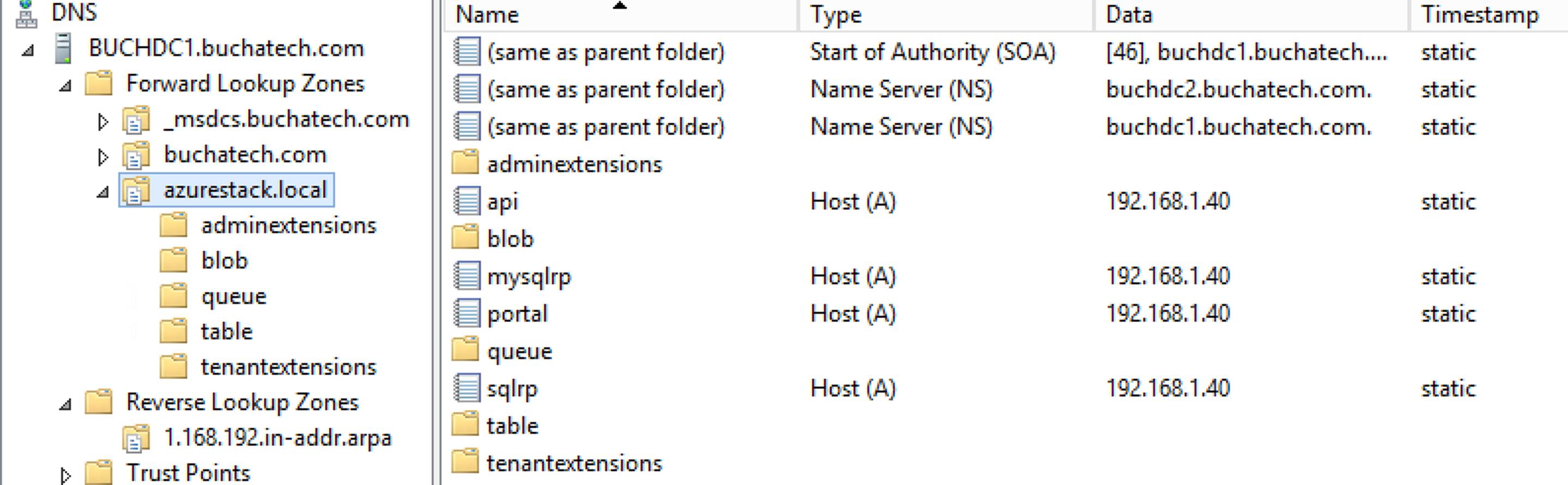
Notice something different I did with my DNS is I did not add *.azurestack.local. I did not do this because it caused any of the storage DNS entries to respond with the PortalExternalIP instead of the ACSExternalIP. Here is a screenshot of my Azure Stack DNS zone in my Buchatech domain:
After adding the DNS records and installing the Azure Stack certificate in the trusted root authority store I was able to access the Azure Stack portal and connect via PowerShell or Visual Studio without VPN. 🙂
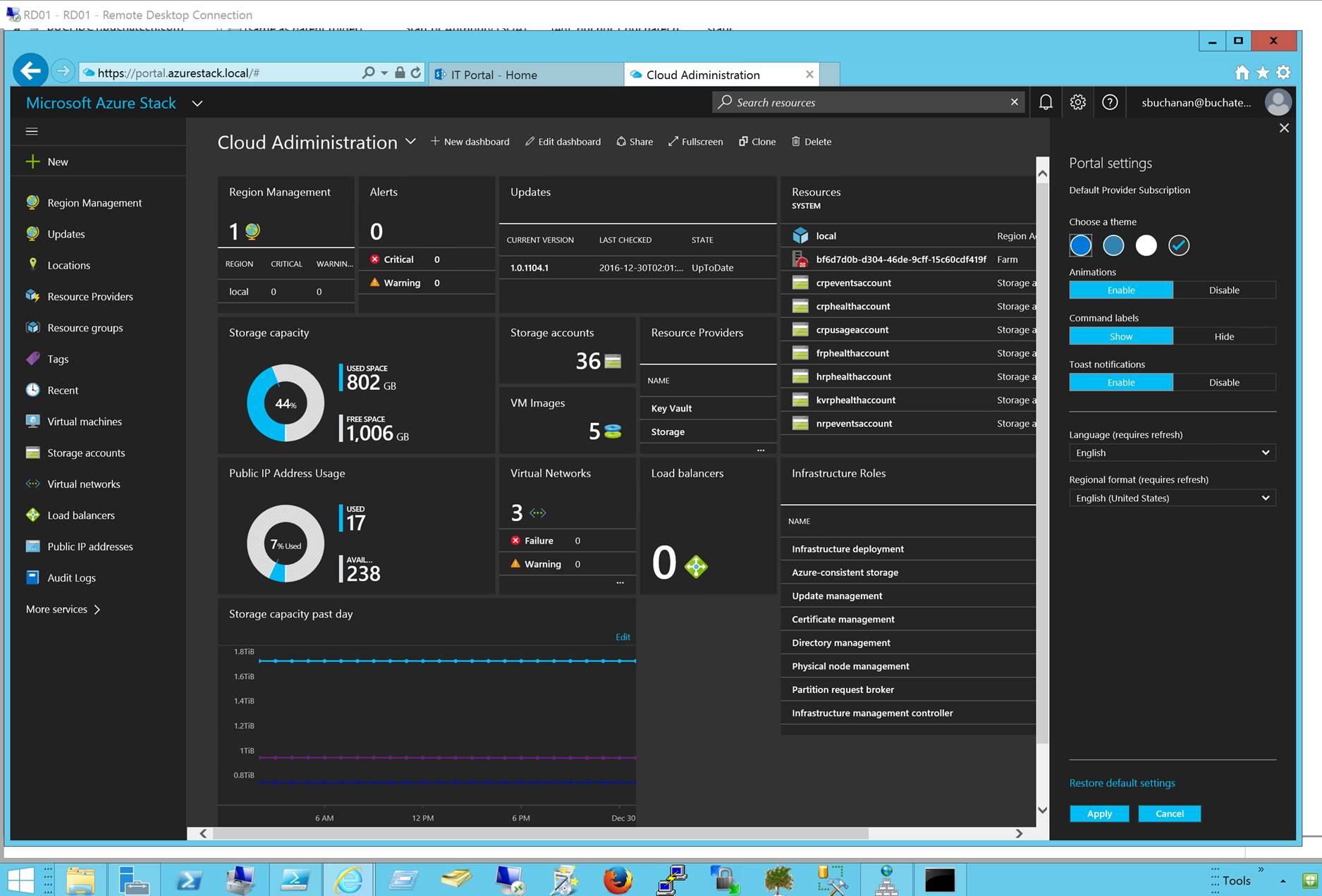
Here is a screenshot of me connecting to Azure Stack’s portal from my Buchatech.com domain on one of my utility servers.
A huge thanks to Ruud for building that PowerShell script. I am excited about bringing access to Azure Stack on my other lab network because this opens up all sorts of possibilities and will net some cool blog posts very soon!
Happy Stacking!